The cryptography is a complex field that needs knowledge of mathematics, electronics, and programming. The need and desire for private and secret communication are necessary for the military communication systems. The study of various ways to disguise messages in order to avoid interception from an unauthorized interception is known as Cryptography.
Components of Cryptography
- Sender
- Encryption
- Network
- Decryption
- Receiver
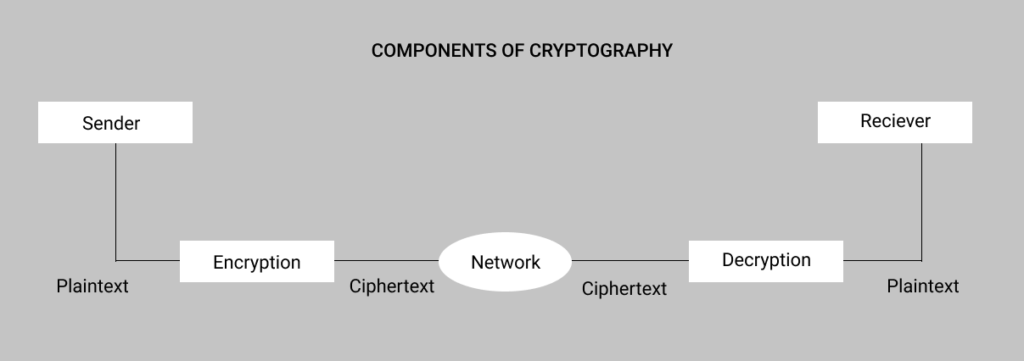
Plaintext : The Original message produced by the sender is called Plaintext.
Ciphertext : The plaintext is transformed into ciphertext.
Decryption : Decryption is a process which is exactly opposite to encryption.
Ciphers : The encryption and decryption algorithm together are referred as to Ciphers.
Key : A key is a value or a number.
Types of Cryptography
- Symmetric Key /Secret key Cryptography :
In the symmetric key Cryptography ,the same key is used by the sender and receiver.It is also called secret key Cryptography.
Advantages :
- It is more efficient than the public key algorithm .It takes less time to encrypt a message using the symmetric key algorithm because the key is smaller size.
- It is used for both encryption and decryption of long messages.
Drawbacks :
- The first drawback is that the sender and receiver both should have unique symmetric key.
- The distribution of keys between two users can be difficult.
- Public Key /Asymmetric Key Cryptography :
The public key Cryptography is also called as the asymmetric key cryptography .This type of cryptography uses two key :
- Private Key
- Public Key
Out of them, the private key is kept by the receiver whereas the public key announced to the public. In this system, the sender uses the public key to encrypt the message to send.
At the receiver, this message is decrypted with the help of the receiver’s private key. The public key is used for encryption is different from the private key is known to everyone but the private is available only to an individual.
Advantages :
- There is no compulsion of using the symmetric key by the sender and receivers.
- The number of keys required reduces tremendously.
Drawbacks :
- The algorithm used are highly complex.
- It takes long time to calculate cipher-text from plaintext.